Complete Guide to Trezor Login
Managing your cryptocurrency securely begins with the Trezor Login. The Trezor Login allows users to connect their hardware wallet, access accounts, and manage transactions with confidence. This guide explores how to perform the Trezor Login, solve common issues, and maximize account security.
Understanding the Trezor Login Process
The Trezor Login requires connecting your Trezor device via USB or WebUSB, then entering your PIN directly on the device. Each Trezor Login ensures your private keys remain offline, offering maximum protection for your digital assets.
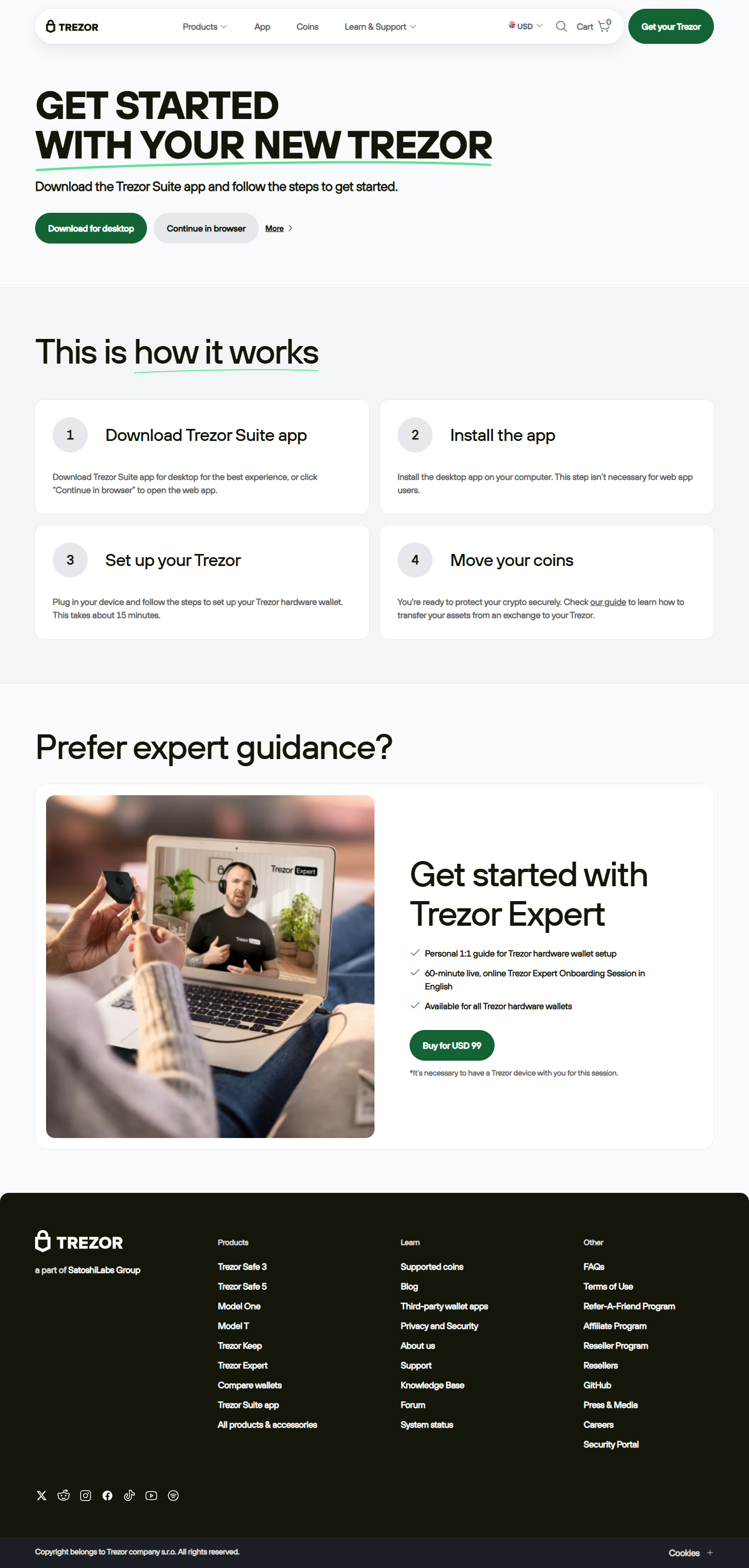
Step-by-Step Trezor Login Instructions
Follow these steps to complete your Trezor Login:
- Open the official Trezor Suite application or visit the official Trezor website.
- Connect your Trezor hardware wallet via USB.
- Select the "Login" option to start the Trezor Login process.
- Enter your PIN on the device when prompted.
- Access your account dashboard securely.
By using the device-based PIN entry, every Trezor Login remains secure against phishing attempts or keyloggers.
Common Trezor Login Issues
Sometimes users face challenges with Trezor Login, such as unrecognized devices, outdated firmware, or browser incompatibility. Updating Trezor Suite, replacing USB cables, or trying a different browser usually resolves Trezor Login problems.
Security Best Practices for Trezor Login
Security is the cornerstone of every Trezor Login. Always verify you’re on the official Trezor platform, enable passphrase protection, and never share your recovery seed. These measures guarantee your Trezor Login remains safe from unauthorized access.
Trezor Login Across Devices
The Trezor Login works seamlessly across desktop, laptop, and mobile (via OTG support). This cross-platform flexibility allows you to manage assets wherever you are, with Trezor Login always ensuring hardware-level protection.
Troubleshooting Trezor Login Problems
If your Trezor Login fails, confirm your USB connection, update your firmware, and restart the Trezor Suite app. For persistent issues, Trezor support offers guidance to restore secure Trezor Login access quickly.
Conclusion: Mastering Trezor Login
The Trezor Login is the secure entry point to managing cryptocurrencies with your hardware wallet. By following official instructions, applying strong security practices, and troubleshooting effectively, every Trezor Login session ensures peace of mind and protection of your assets.